GlassWorm malware hits 400+ code repos on GitHub, npm, VSCode, OpenVSX
The GlassWorm supply-chain campaign has returned with a new, coordinated attack that targeted hundreds of packages, repositories, and extensions on GitHub, npm, and VSCode/OpenVSX extensions.
Researchers at Aikido, Socket, Step Security, and the OpenSourceMalware community have collectively identified 433 compromised components this month in attacks attributed to GlassWorm.
Evidence of a single threat actor running the GlassWorm campaigns across multiple open-source repositories is provided by the use of the same Solana blockchain address used for command-and-control (C2) activity, identical or functionally similar payloads, and shared infrastructure.
GlassWorm was first observed last October, with attackers using “invisible” Unicode characters to hide malicious code that harvested cryptocurrency wallet data and developer credentials.
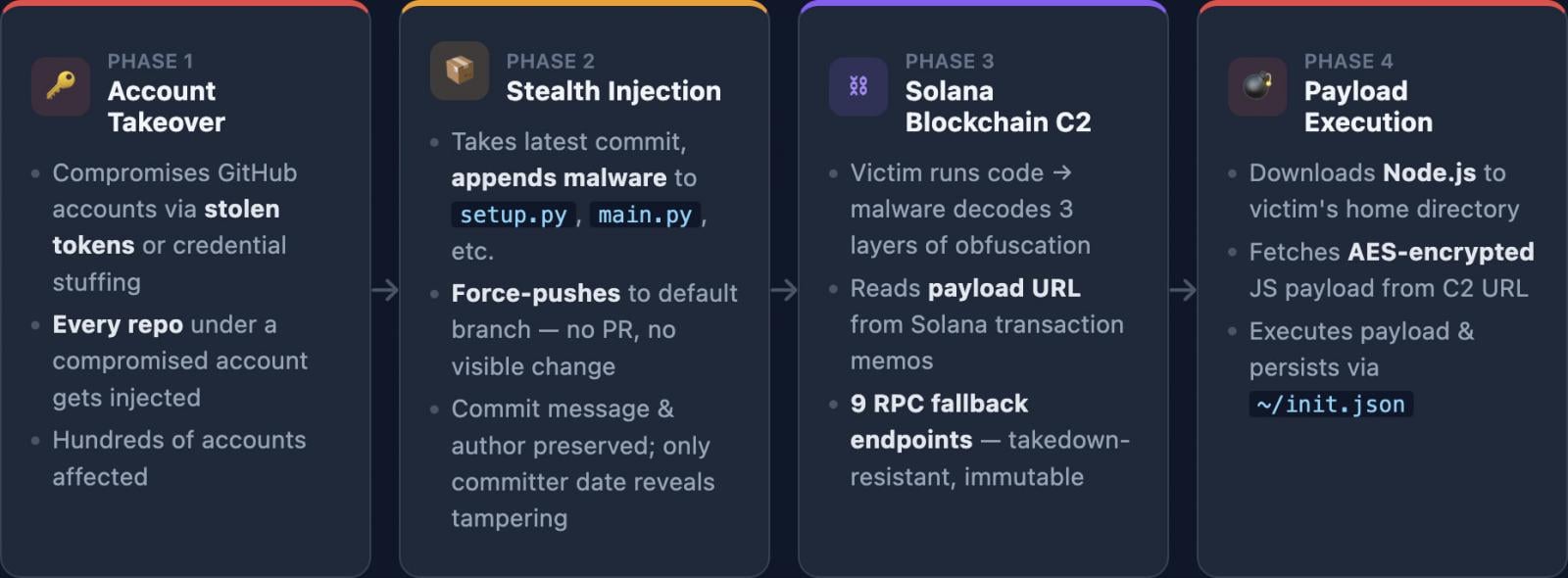
The campaign continued with multiple waves and expanded to Microsoft’s official Visual Studio Code marketplace and the OpenVSX registry used by unsupported IDEs, as discovered by Secure Annex’s researcher, John Tuckner.
macOS systems were also targeted, introducing trojanized clients for Trezor and Ledger, and later targeted developers via compromised OpenVSX extensions.
The latest GlassWorm attack wave is far more extensive, though, and spread to:
- 200 GitHub Python repositories
- 151 GitHub JS/TS repositories
- 72 VSCode/OpenVSX extensions
- 10 npm packages
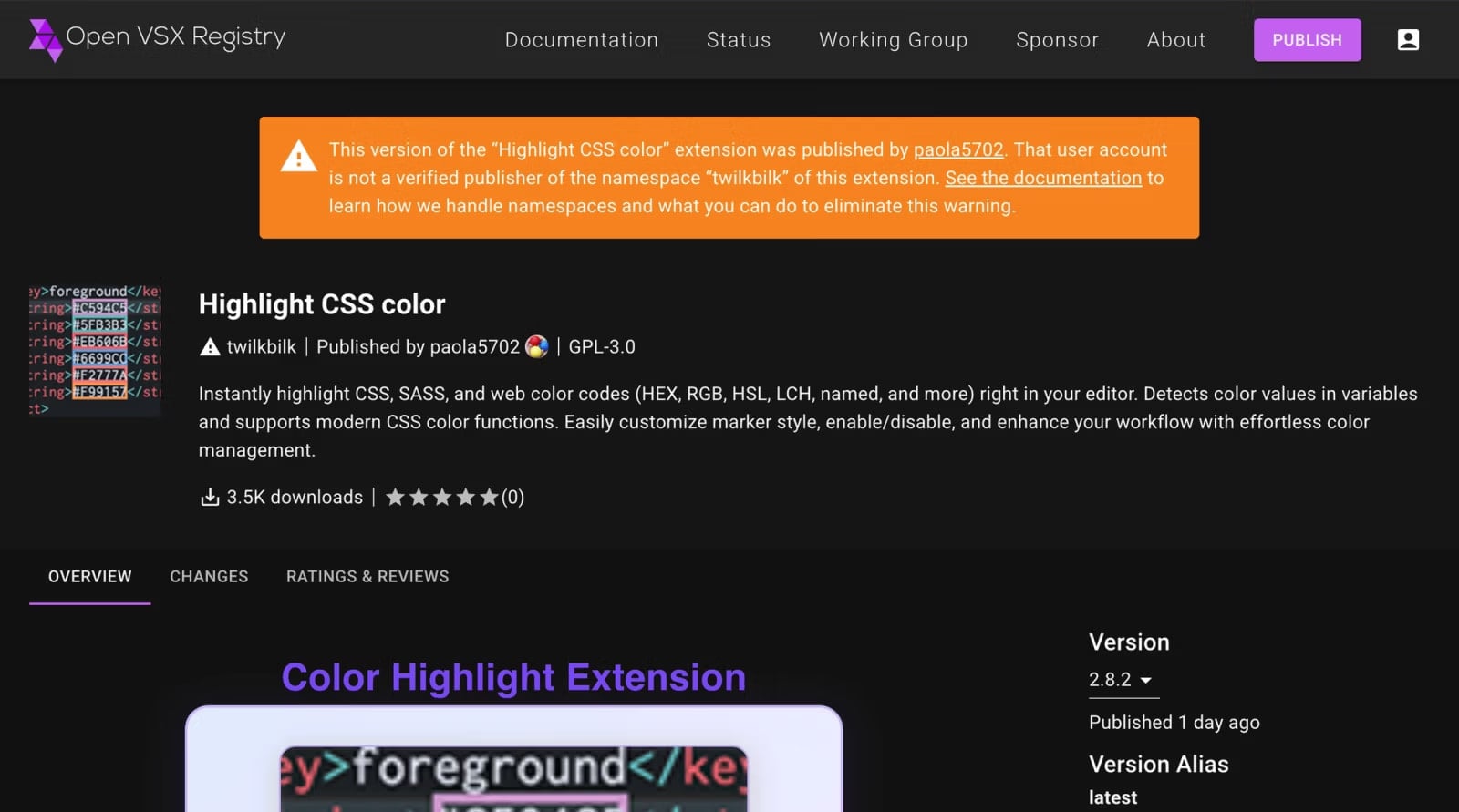
Initial compromise occurs on GitHub, where accounts are compromised to force-push malicious commits.
Then, malicious packages and extensions are published on npm and VSCode/OpenVSX, featuring obfuscated code (invisible Unicode characters) to evade detection.
Source: Aikido
Across all platforms, the Solana blockchain is queried every five seconds for new instructions. According to Step Security, between November 27, 2025, and March 13, 2026, there were 50 new transactions, mostly to update the payload URL.
The instructions were embedded as memos in the transactions and led to downloading the Node.js runtime and executing a JavaScript-based information stealer.
Source: Step Security
The malware targets cryptocurrency wallet data, credentials, and access tokens, SSH keys, and developer environment data.
Analysis of code comments indicates that GlassWorm is orchestrated by Russia-speaking threat actors. Additionally, the malware skips execution if the Russian locale is found on the system. However, this is insufficient data for confident attribution.
Step Security advises developers who install Python packages directly from GitHub or run cloned repositories to check for signs of compromise by searching their codebase for the marker variable “lzcdrtfxyqiplpd,” an indicator of the GlassWorm malware.
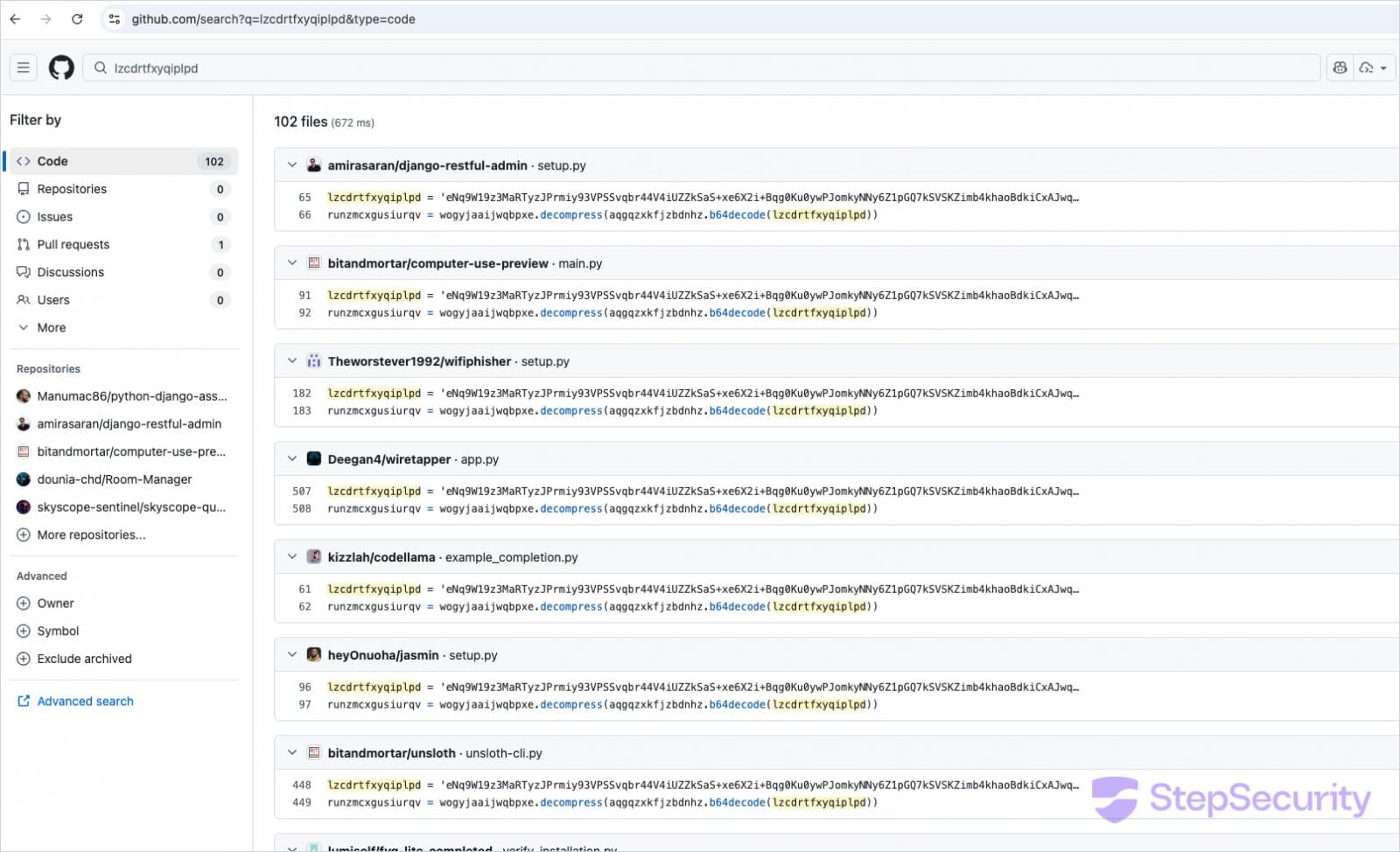
Source: Step Security
They also recommend inspecting systems for the presence of the ~/init.json file, which is used for persistence, as well as unexpected Node.js installations in the home directory (e.g., ~/node-v22*).
Additionally, developers should look for suspicious i.js files in recently cloned projects and review Git commit histories for anomalies, such as commits where the committer date is significantly newer than the original author date.
First Appeared on
Source link