Quantum Cryptography Pioneers Win Turing Award
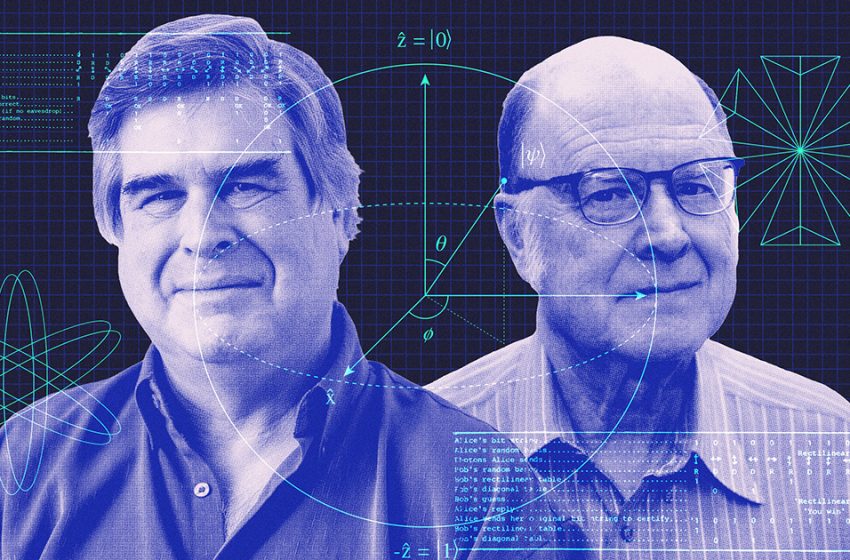
In the early 1970s, Wiesner abruptly abandoned physics research and joined the California counterculture, and his revolutionary paper remained unpublished for nearly 15 years. (Wiesner later embraced religion, moved to Israel, and became a construction worker. He died in 2021.) Bennett, meanwhile, eventually landed a job at IBM, where he developed a new theory of reversible computation. But he couldn’t get Wiesner’s idea out of his mind. He tried to interest other researchers for a decade, to no avail, until he met Brassard in Puerto Rico.
Quantum Secrets
As they bobbed in the waves on that fateful day, Brassard pointed out a glaring problem with the quantum money scheme. It would be impossible to counterfeit banknotes, but it would also be difficult to use them, since only the person who created a bill would be able to check that it was valid. Brassard suggested that it might be possible to patch this problem by combining Wiesner’s scheme with techniques from cryptography. By the time the duo returned to shore 10 minutes later, they had settled on the key ideas in what would later become their first joint paper.
After that initial encounter, Bennett and Brassard would visit each other occasionally to swap ideas. They could only afford to devote so much time to their shared interest in the obscure subject of quantum information.
“In those days, it was nobody’s day job,” Bennett said.
The duo began to wonder whether they could harness quantum measurement disturbance to keep secret messages safe from eavesdroppers. Cryptographers already knew one encryption scheme that was perfectly secure in principle. But it required the sender and receiver, typically called Alice and Bob, to meet in person and choose a long string of random bits to use as a secret encryption key. What’s more, they’d need to use a separate key for each new message. These restrictions were too cumbersome for most applications. More practical encryption schemes avoided the need for in-person meetings but relied on unproven assumptions about the difficulty of certain math problems.
In 1983, Bennett and Brassard devised a new quantum approach to private communication. In their scheme, now known as BB84, Alice and Bob would establish a shared secret key by sending and measuring photons, the quantum particles that constitute light, without ever needing to meet in person. They could then use that key to encrypt a message. The method again made use of quantum measurement disturbance: Any eavesdropper who tried to snoop on the quantum transmissions would disrupt them, learning nothing and alerting Alice and Bob to their presence. It also didn’t rely on any mathematical assumptions. Not even an eavesdropper who could magically solve the world’s hardest math problems would learn the secret key.
Teleporting Forward
Bennett and Brassard’s quantum key distribution paper would become one of the most famous works in quantum information science. But at the time, few took notice. So the duo eventually decided to build an experimental demonstration. “I wanted to show that it’s possible, that it’s not just nonsense from a theoretician,” Brassard said.
With no budget and little experience in experimental physics, Bennett and Brassard’s team had to improvise. At one point Bennett and his colleague John Smolin bought a sheet of black velvet from a fabric store to block out stray light, telling the confused shop clerk that they needed it for quantum cryptography. (Bennett later repurposed the velvet for a hat.) They finally got the experiment working in October 1989 — 10 years to the day after Bennett and Brassard’s first meeting in Puerto Rico. Their apparatus demonstrated quantum key distribution across a distance of 30 centimeters. More recent demonstrations using satellite links have implemented their method over more than 1,000 kilometers.
In 1993, Bennett, Brassard, and four other researchers published another iconic paper that showed how to use a bizarre quantum phenomenon called entanglement to “teleport” the state of one quantum particle onto another. (Though the name calls to mind Captain Kirk getting beamed up to the Enterprise, quantum teleportation transmits only information, not matter.) It was one of the first examples of how entanglement could serve as a resource for information processing.
By that point, quantum information science was attracting a bit of buzz. It really took off a year later. Digital encryption often relies on the assumption that it’s hard for a computer to break a large number into its prime factors. But in 1994, the applied mathematician Peter Shor devised a quantum algorithm that could quickly do just that. Shor’s milestone result underscored the importance of quantum encryption methods that didn’t require assumptions about mathematical difficulty.
“Shor’s algorithm made our idea unavoidable,” Brassard said.
In the 30 years since Shor’s discovery, interest and investment in quantum information science have skyrocketed. Researchers have raced to build powerful quantum computers and identified connections to seemingly unrelated topics in fundamental physics. There’s also been a surge of new interest in quantum cryptography. Until a few years ago, researchers believed that quantum tricks were only useful for a few special cryptographic tasks like key distribution. But a recent line of work has offered tantalizing hints that the scope of quantum cryptography might be much broader. Bennett and Brassard have followed these new developments with interest.
“That is a very fascinating idea,” Bennett said. “It might be a way where there’s a quantum rescue from the quantum disaster of Shor’s algorithm.”
Editor’s note: Scott Aaronson is a member of Quanta Magazine’s advisory board.
First Appeared on
Source link